Fraudsters are continuing to send victims their own passwords in sextortion scam
15 May 2019 10:17 AM
A sextortion phishing scam, first identified by the National Fraud Intelligence Bureau (NFIB) in July 2018, continues to be reported to Action Fraud in high numbers.
Fraudsters are sending victims their own passwords in an attempt to trick them into believing they have been filmed on their computer watching porn and demanding payment.
In May alone, Action Fraud has received over 149 crime reports and 1,443 reports to our phishing reporting tool. Many victims report receiving multiple emails over a short period of time.
The emails contain the victim’s own password in the subject line and demands payment in Bitcoin after claiming that the victim has been filmed on their computer watching porn.
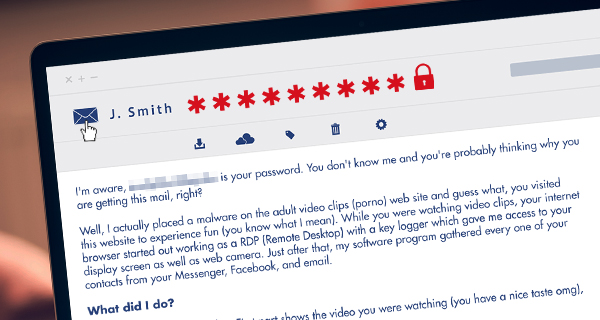
An example email reads;
I'm aware, XXXXXX is your password. You don't know me and you're probably thinking why you are getting this mail, right?
Well, I actually placed a malware on the adult video clips (porno) web site and guess what, you visited this website to experience fun (you know what I mean). While you were watching video clips, your internet browser started out working as a RDP (Remote Desktop) with a key logger which gave me access to your display screen as well as web camera. Just after that, my software program gathered every one of your contacts from your Messenger, Facebook, and email.
What did I do?
I made a double-screen video. First part shows the video you were watching (you have a nice taste omg), and 2nd part displays the recording of your webcam.
Exactly what should you do?
Well, I believe, $2900 is a fair price tag for our little secret. You'll make the payment by Bitcoin (if you do not know this, search "how to buy bitcoin" in Google).
BTC Address: 1HpXtDRumKRhaFTXXXXXXXXXX
(It is cAsE sensitive, so copy and paste it)
Important:
You now have one day to make the payment. (I have a special pixel within this email message, and now I know that you have read this e mail). If I do not receive the BitCoins, I will definately send out your video recording to all of your contacts including close relatives, co-workers, and many others. Nevertheless, if I receive the payment, I'll destroy the video immidiately. If you need evidence, reply with "Yes!" and I will send your video to your 10 friends. It is a non-negotiable offer, therefore do not waste my time and yours by responding to this message.
Suspected data breach
Action Fraud suspects that the fraudsters may have gained victim’s passwords from an old data breach.
After running some of the victim’s email addresses through ‘Have i been pwned?’, a website that allows people to check if their account has been compromised in a data breach, Action Fraud found that almost all of the accounts were at risk.
How to protect yourself
- Don’t reply to the email, or be pressured into paying: it only highlights that you’re vulnerable and you could be targeted again. The police advise that you do not pay criminals. Try flagging the email as spam/junk if you receive it multiple times.
- Perform password resets as soon as possible on any accounts where you’ve used the password mentioned in the email. Always use a strong, separate password for important accounts, such as your email. Where available, enable Two-Factor Authentication (2FA).
- Always install the latest software & app updates. Install, or enable, anti-virus software on your laptops & computers and keep it updated.
- If you have received one of these emails and paid the fine, report it to your local police force. If you have not paid, report the email as a phishing attempt to Action Fraud.